![Dmitry Bestuzhev on X: "Hash cracker hashkiller[.]co[.]uk/md5-decrypter.aspx includes a hidden cryptominer on its site. You crack, they mine. #CoinHive #cryptominer https://t.co/qfsm1m4pjb" / X Dmitry Bestuzhev on X: "Hash cracker hashkiller[.]co[.]uk/md5-decrypter.aspx includes a hidden cryptominer on its site. You crack, they mine. #CoinHive #cryptominer https://t.co/qfsm1m4pjb" / X](https://pbs.twimg.com/media/DUQn1SnXUAURB1t.jpg:large)
Dmitry Bestuzhev on X: "Hash cracker hashkiller[.]co[.]uk/md5-decrypter.aspx includes a hidden cryptominer on its site. You crack, they mine. #CoinHive #cryptominer https://t.co/qfsm1m4pjb" / X

Password hacking / password cracking – www.hashkiller.co.uk | University of South Wales: Cyber University of the year: Four years running: 2019, 2020, 2021, 2022

Amazon.com: Uncanny Coincidence: Book 9 in the Jerry McNeal series (A Paranormal Snapshot): 9781951386269: Burton, Sherry A.: Books

Sour Diesel x Purple Punch Primo Infused Preroll 1.3g | KGB Reserve | PRIMO + 20% Hash Infused Pre Roll

It's Sunday funday y'all! That means crispy Buffalo wings, and this killer kielbasa dog with hash, slaw, and mustard Q! And don't forget… | Instagram

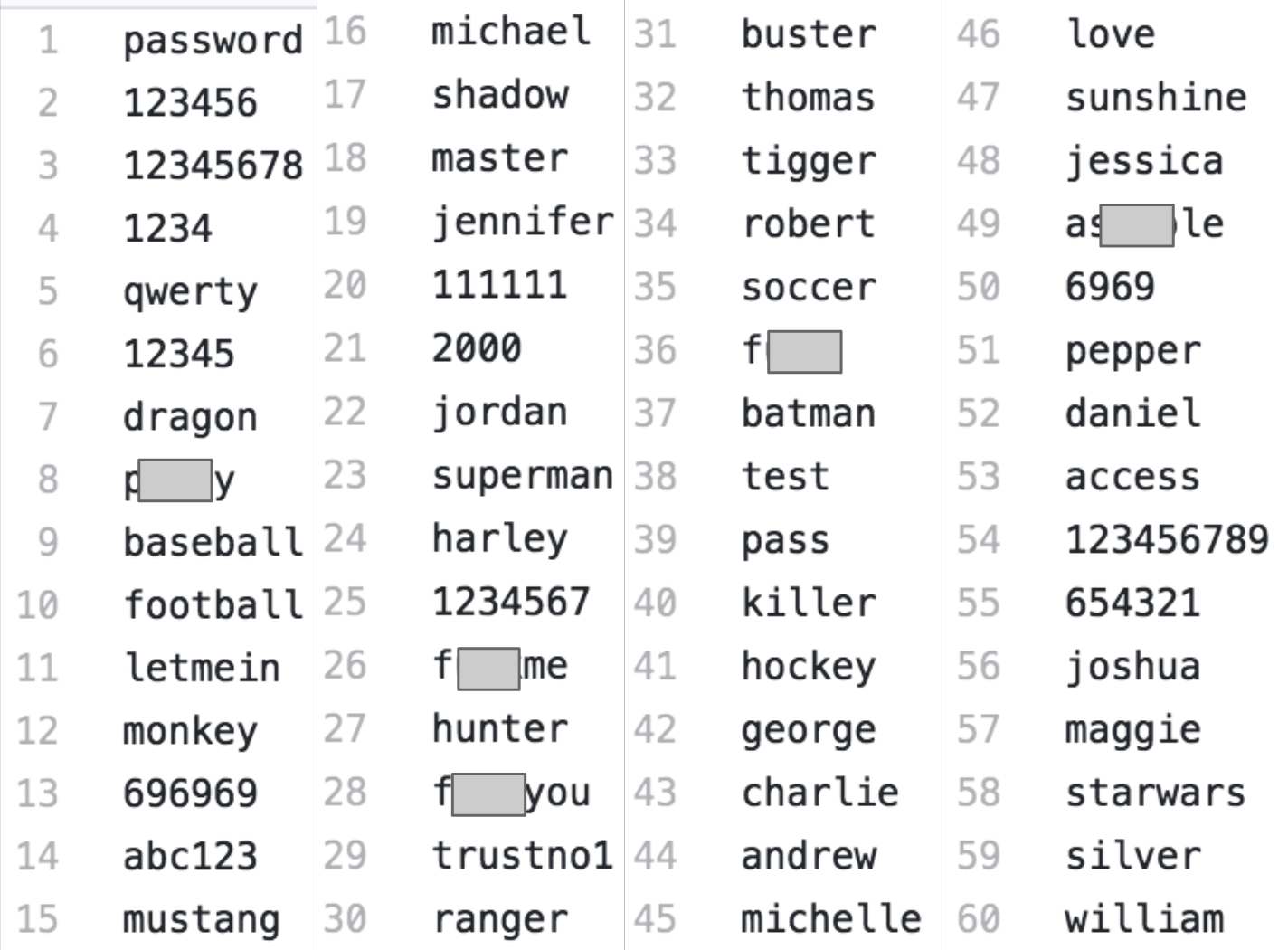
Password Cracking – What is a password hash? | University of South Wales: Cyber University of the year: Four years running: 2019, 2020, 2021, 2022

Anime Demon Killer Hash Pull Sword Poster Poster Decorative Painting Canvas Wall Art Living Room Posters Bedroom Painting 20×30inch(50×75cm) : Amazon.ca: Home

BleepingComputer on X: "Once a threat actor gains access to the NTLM hash, it's as simple as running it through Hashcat to dehash the password. Now the threat actor has both the



![Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book] Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book]](https://www.oreilly.com/api/v2/epubs/9781787121829/files/assets/714fa5ac-a3a0-4378-b325-97dee1e71141.png)



/cdn.vox-cdn.com/uploads/chorus_image/image/39137722/hashex1.0.jpg)

























:no_upscale()/cdn.vox-cdn.com/uploads/chorus_asset/file/24899264/armons_1.jpg)

![Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book] Hashkiller - Kali Linux - An Ethical Hacker's Cookbook [Book]](https://www.oreilly.com/api/v2/epubs/9781787121829/files/assets/7a0893f5-8a61-4c69-9be4-c06c4d78fe7d.png)
:max_bytes(150000):strip_icc()/latke-breakfast-hash-FT-RECIPE1220-3bd7d7c1768d4d9eb16999f522bbc2ea.jpg)
